While in Red Hat Enterprise Linux 7 Docker was officially supported, on the new release of this open source operating system, it has been replaced by a series of other tools developed by Red Hat itself: buildah and podman. By the use of an external repository, however, it's still possible to install Docker CE (Community Edition). Configuring Docker to accept remote connections can be done with the docker.service systemd unit file for Linux distributions using systemd, such as recent versions of RedHat, CentOS, Ubuntu and SLES, or with the daemon.json file which is recommended for Linux distributions that do not use systemd. Install AWS CLI in Linux (RHEL/CentOS 7/8) Also Read: Best Steps for s3cmd configuration in Linux (CentOS/RedHat 7) Step 1: Prerequisites. A)You need to have a running RHEL/CentOS 7/8 System. Install Docker CE: yum install docker-ce. Systemctl start docker systemctl enable docker Test Docker installation: docker run hello-world. Remove old versions of Docker: apt-get remove docker docker-engine docker.io. If you are installing on Ubuntu 14.04, install the linux-image-extra package. Red Hat Enterprise Linux Atomic Host 7 Use podman, skopeo, and buildah to work with containers in Red Hat Enterprise Linux 7 and RHEL Atomic Host Red Hat Atomic Host Documentation Team appinfra-docs@redhat.com.
- Install Docker Linux Redhat
- Install Docker On Redhat Linux 7
- Install Docker On Redhat 5
- Install Docker On Redhat 7.9
You can configure automatic log upload for continuous reports in Cloud App Security using a Docker on an on-premises Ubuntu, Red Hat Enterprise Linux (RHEL), or CentOS server.
Install Docker Linux Redhat
Prerequisites
OS:
- Ubuntu 14.04, 16.04, and 18.04
- RHEL 7.2 or higher
- CentOS 7.2 or higher
Disk space: 250 GB
CPU: 2
RAM: 4 GB
Set your firewall as described in Network requirements
Note
If you have an existing log collector and want to remove it before deploying it again, or if you simply want to remove it, run the following commands:
Log collector performance
The Log collector can successfully handle log capacity of up to 50 GB per hour. The main bottlenecks in the log collection process are:
Network bandwidth - Your network bandwidth determines the log upload speed.
I/O performance of the virtual machine - Determines the speed at which logs are written to the log collector's disk. The log collector has a built-in safety mechanism that monitors the rate at which logs arrive and compares it to the upload rate. In cases of congestion, the log collector starts to drop log files. If your setup typically exceeds 50 GB per hour, it's recommended that you split the traffic between multiple log collectors.
Set up and configuration
Step 1 – Web portal configuration: Define data sources and link them to a log collector
Go to the Automatic log upload settings page.
- In the Cloud App Security portal, click the settings icon followed by Log collectors.
For each firewall or proxy from which you want to upload logs, create a matching data source.
- Click Add data source.
- Name your proxy or firewall.
- Select the appliance from the Source list. If you select Custom log format to work with a network appliance that isn't listed, see Working with the custom log parser for configuration instructions.
- Compare your log with the sample of the expected log format. If your log file format doesn't match this sample, you should add your data source as Other.
- Set the Receiver type to either FTP, FTPS, Syslog – UDP, or Syslog – TCP, or Syslog – TLS.
Note
Integrating with secure transfer protocols (FTPS and Syslog – TLS) often requires additional settings or your firewall/proxy.
f. Repeat this process for each firewall and proxy whose logs can be used to detect traffic on your network. It's recommended to set up a dedicated data source per network device to enable you to:
- Monitor the status of each device separately, for investigation purposes.
- Explore Shadow IT Discovery per device, if each device is used by a different user segment.
- Click Add data source.
Go to the Log collectors tab at the top.
- Click Add log collector.
- Give the log collector a name.
- Enter the Host IP address of the machine you'll use to deploy the Docker. The host IP address can be replaced with the machine name, if there is a DNS server (or equivalent) that will resolve the host name.
- Select all Data sources that you want to connect to the collector, and click Update to save the configuration.
Further deployment information will appear. Copy the run command from the dialog. You can use the copy to clipboard icon.
Export the expected data source configuration. This configuration describes how you should set the log export in your appliances.
Note
- A single Log collector can handle multiple data sources.
- Copy the contents of the screen because you will need the information when you configure the Log Collector to communicate with Cloud App Security. If you selected Syslog, this information will include information about which port the Syslog listener is listening on.
- For users sending log data via FTP for the first time, we recommend changing the password for the FTP user. For more information, see Changing the FTP password.
Step 2 – On-premises deployment of your machine
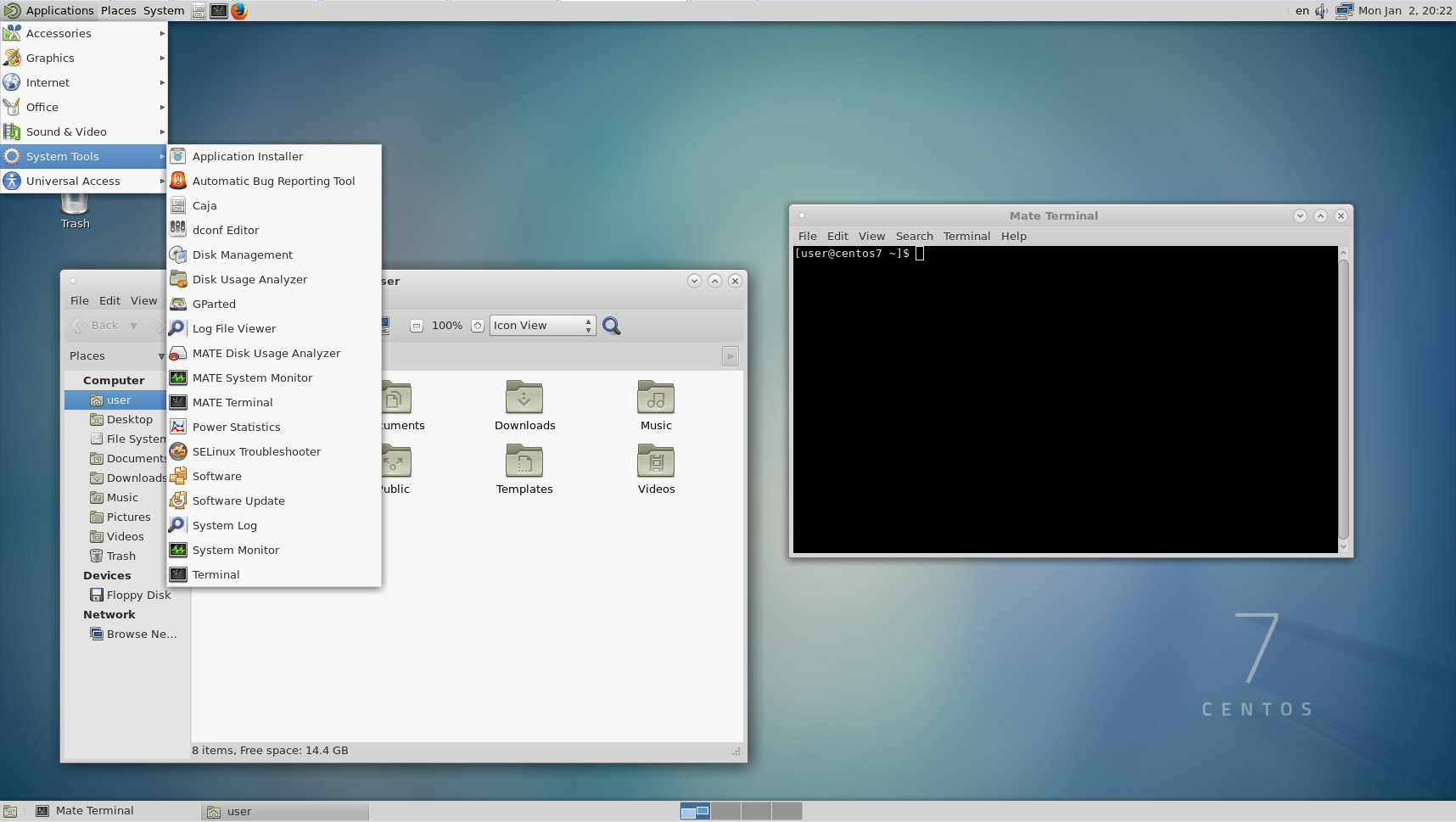
The following steps describe the deployment in Ubuntu.
Note
The deployment steps for other supported platforms may be slightly different.
Open a terminal on your Ubuntu machine.
Change to root privileges using the command:
sudo -iTo bypass a proxy in your network, run the following two commands:
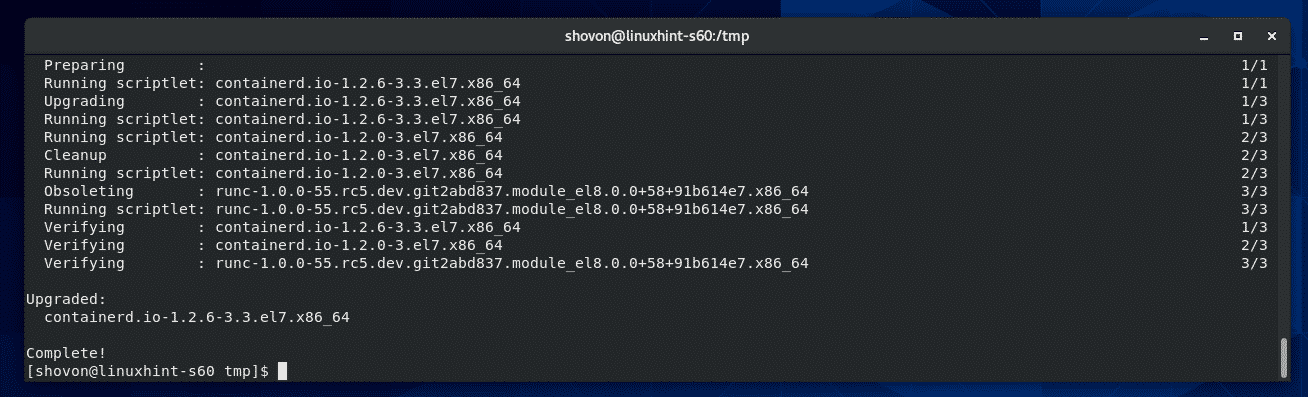
If you accept the software license terms, uninstall old versions and install Docker CE by running the commands appropriate for your environment:
Remove old versions of Docker:
yum erase docker docker-engine docker.ioInstall Docker engine prerequisites:
yum install -y yum-utilsAdd Docker repository:
Install Docker engine:
yum -y install docker-ceStart Docker
Test Docker installation:
docker run hello-world
Remove old versions of Docker:
yum erase docker docker-engine docker.ioInstall Docker engine prerequisites:
Add Docker repository:
Install dependencies:
Install Docker engine:
sudo yum install docker-ceStart Docker
Test Docker installation:
docker run hello-world
Remove the container-tools module:
yum module remove container-toolsAdd the Docker CE repository:
yum-config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repoModify the yum repo file to use CentOS 8/RHEL 8 packages:
sed -i s/7/8/g /etc/yum.repos.d/docker-ce.repoInstall Docker CE:
yum install docker-ceStart Docker
Test Docker installation:
docker run hello-world
Remove old versions of Docker:
apt-get remove docker docker-engine docker.ioIf you are installing on Ubuntu 14.04, install the linux-image-extra package.
Install Docker engine prerequisites:
Verify that the apt-key fingerprint UID is docker@docker.com:
apt-key fingerprint | grep uidInstall Docker engine:
Test Docker installation:
docker run hello-world
Deploy the collector image on the hosting machine by importing the collector configuration. Import the configuration by copying the run command generated in the portal. If you need to configure a proxy, add the proxy IP address and port number. For example, if your proxy details are 192.168.10.1:8080, your updated run command is:
Verify that the collector is running properly with the following command:
docker logs <collector_name>
You should see the message: Finished successfully!
Step 3 - On-premises configuration of your network appliances
Configure your network firewalls and proxies to periodically export logs to the dedicated Syslog port or the FTP directory according to the directions in the dialog. For example:
Step 4 - Verify the successful deployment in the Cloud App Security portal
Check the collector status in the Log collector table and make sure the status is Connected. If it's Created, it's possible the log collector connection and parsing haven't completed.
You can also go to the Governance log and verify that logs are being periodically uploaded to the portal.
Alternatively, you can check the log collector status from within the docker container using the following commands:
- Log in to the container by using this command:
docker exec -it <Container Name> bash - Verify the log collector status using this command:
collector_status -p
If you have problems during deployment, see Troubleshooting Cloud Discovery.
Optional - Create custom continuous reports
Verify that the logs are being uploaded to Cloud App Security and that reports are generated. After verification, create custom reports. You can create custom discovery reports based on Azure Active Directory user groups. For example, if you want to see the cloud use of your marketing department, import the marketing group using the import user group feature. Then create a custom report for this group. You can also customize a report based on IP address tag or IP address ranges.
- In the Cloud App Security portal, under the Settings cog, select Cloud Discovery settings, and then select Continuous reports.
- Click the Create report button and fill in the fields.
- Under the Filters you can filter the data by data source, by imported user group, or by IP address tags and ranges.
Next steps
If you run into any problems, we're here to help. To get assistance or support for your product issue, please open a support ticket.
Estimated reading time: 15 minutes
This section contains optional procedures for configuring Linux hosts to workbetter with Docker.
Manage Docker as a non-root user
The Docker daemon binds to a Unix socket instead of a TCP port. By defaultthat Unix socket is owned by the user root and other users can only access itusing sudo. The Docker daemon always runs as the root user.
If you don’t want to preface the docker command with sudo, create a Unixgroup called docker and add users to it. When the Docker daemon starts, itcreates a Unix socket accessible by members of the docker group.
Warning
The docker group grants privileges equivalent to the rootuser. For details on how this impacts security in your system, seeDocker Daemon Attack Surface.
Note:
To run Docker without root privileges, seeRun the Docker daemon as a non-root user (Rootless mode).
To create the docker group and add your user:
Create the
dockergroup.Add your user to the
dockergroup.Log out and log back in so that your group membership is re-evaluated.
If testing on a virtual machine, it may be necessary to restart the virtual machine for changes to take effect.
On a desktop Linux environment such as X Windows, log out of your session completely and then log back in.
On Linux, you can also run the following command to activate the changes to groups:
Verify that you can run
dockercommands withoutsudo.This command downloads a test image and runs it in a container. When thecontainer runs, it prints an informational message and exits.
If you initially ran Docker CLI commands using
sudobefore addingyour user to thedockergroup, you may see the following error,which indicates that your~/.docker/directory was created withincorrect permissions due to thesudocommands.To fix this problem, either remove the
~/.docker/directory(it is recreated automatically, but any custom settingsare lost), or change its ownership and permissions using thefollowing commands:
Configure Docker to start on boot
Most current Linux distributions (RHEL, CentOS, Fedora, Debian, Ubuntu 16.04 andhigher) use systemd to manage which services start when the systemboots. On Debian and Ubuntu, the Docker service is configured to start on bootby default. To automatically start Docker and Containerd on boot for otherdistros, use the commands below:
To disable this behavior, use disable instead.
If you need to add an HTTP Proxy, set a different directory or partition for theDocker runtime files, or make other customizations, seecustomize your systemd Docker daemon options.
Use a different storage engine
For information about the different storage engines, seeStorage drivers.The default storage engine and the list of supported storage engines depend onyour host’s Linux distribution and available kernel drivers.
Configure default logging driver
Docker provides the capability tocollect and view log data from all containers running on a host via a series oflogging drivers. The default logging driver, json-file, writes log data toJSON-formatted files on the host filesystem. Over time, these log files expandin size, leading to potential exhaustion of disk resources.
To alleviate such issues, either configure the json-file logging driver toenable log rotation, use analternative logging driversuch as the “local” logging driverthat performs log rotation by default, or use a logging driver that sendslogs to a remote logging aggregator.
Configure where the Docker daemon listens for connections
By default, the Docker daemon listens for connections on a UNIX socket to acceptrequests from local clients. It is possible to allow Docker to accept requestsfrom remote hosts by configuring it to listen on an IP address and port as wellas the UNIX socket. For more detailed information on this configuration optiontake a look at “Bind Docker to another host/port or a unix socket” section ofthe Docker CLI Reference article.
Secure your connection
Before configuring Docker to accept connections from remote hosts it is critically important that youunderstand the security implications of opening docker to the network. If steps are not taken to secure the connection, it is possible for remote non-root users to gain root access on the host. For more information on how to use TLS certificates to secure this connection, check this article on how to protect the Docker daemon socket.
Configuring Docker to accept remote connections can be done with the docker.servicesystemd unit file for Linux distributions using systemd, such as recent versionsof RedHat, CentOS, Ubuntu and SLES, or with the daemon.json file which isrecommended for Linux distributions that do not use systemd.
systemd vs daemon.json
Configuring Docker to listen for connections using both the systemd unit file and the daemon.json file causes a conflict that prevents Docker from starting.
Configuring remote access with systemd unit file
Use the command
sudo systemctl edit docker.serviceto open an override file fordocker.servicein a text editor.Add or modify the following lines, substituting your own values.
Save the file.
Reload the
systemctlconfiguration.Restart Docker.
Check to see whether the change was honored by reviewing the output of
netstatto confirmdockerdis listening on the configured port.
Configuring remote access with daemon.json
Set the
hostsarray in the/etc/docker/daemon.jsonto connect to the UNIX socket and an IP address, as follows:Restart Docker.
Check to see whether the change was honored by reviewing the output of
netstatto confirmdockerdis listening on the configured port.
Enable IPv6 on the Docker daemon
To enable IPv6 on the Docker daemon, seeEnable IPv6 support.
Troubleshooting
Kernel compatibility
Docker cannot run correctly if your kernel is older than version 3.10 or if itis missing some modules. To check kernel compatibility, you can download andrun the check-config.shscript.
The script only works on Linux, not macOS.
Cannot connect to the Docker daemon
If you see an error such as the following, your Docker client may be configuredto connect to a Docker daemon on a different host, and that host may not bereachable.
To see which host your client is configured to connect to, check the value ofthe DOCKER_HOST variable in your environment.
If this command returns a value, the Docker client is set to connect to aDocker daemon running on that host. If it is unset, the Docker client is set toconnect to the Docker daemon running on the local host. If it is set in error,use the following command to unset it:
You may need to edit your environment in files such as ~/.bashrc or~/.profile to prevent the DOCKER_HOST variable from being seterroneously.
If DOCKER_HOST is set as intended, verify that the Docker daemon is runningon the remote host and that a firewall or network outage is not preventing youfrom connecting.
IP forwarding problems
If you manually configure your network using systemd-network with systemdversion 219 or higher, Docker containers may not be able to access your network.Beginning with systemd version 220, the forwarding setting for a given network(net.ipv4.conf.<interface>.forwarding) defaults to off. This settingprevents IP forwarding. It also conflicts with Docker’s behavior of enablingthe net.ipv4.conf.all.forwarding setting within containers.
To work around this on RHEL, CentOS, or Fedora, edit the <interface>.networkfile in /usr/lib/systemd/network/ on your Docker host(ex: /usr/lib/systemd/network/80-container-host0.network) and add thefollowing block within the [Network] section.
This configuration allows IP forwarding from the container as expected.
DNS resolver found in resolv.conf and containers can't use it
Linux systems which use a GUI often have a network manager running, which uses adnsmasq instance running on a loopback address such as 127.0.0.1 or127.0.1.1 to cache DNS requests, and adds this entry to/etc/resolv.conf. The dnsmasq service speeds upDNS look-ups and also provides DHCP services. This configuration does not workwithin a Docker container which has its own network namespace, becausethe Docker container resolves loopback addresses such as 127.0.0.1 toitself, and it is very unlikely to be running a DNS server on its ownloopback address.
If Docker detects that no DNS server referenced in /etc/resolv.conf is a fullyfunctional DNS server, the following warning occurs and Docker uses the publicDNS servers provided by Google at 8.8.8.8 and 8.8.4.4 for DNS resolution.
If you see this warning, first check to see if you use dnsmasq:
If your container needs to resolve hosts which are internal to your network, thepublic nameservers are not adequate. You have two choices:
Install Docker On Redhat Linux 7
- You can specify a DNS server for Docker to use, or
- You can disable
dnsmasqin NetworkManager. If you do this, NetworkManageradds your true DNS nameserver to/etc/resolv.conf, but you lose thepossible benefits ofdnsmasq.
You only need to use one of these methods.
Specify DNS servers for Docker
The default location of the configuration file is /etc/docker/daemon.json. Youcan change the location of the configuration file using the --config-filedaemon flag. The documentation below assumes the configuration file is locatedat /etc/docker/daemon.json.
Create or edit the Docker daemon configuration file, which defaults to
/etc/docker/daemon.jsonfile, which controls the Docker daemonconfiguration.Add a
dnskey with one or more IP addresses as values. If the file hasexisting contents, you only need to add or edit thednsline.If your internal DNS server cannot resolve public IP addresses, include atleast one DNS server which can, so that you can connect to Docker Hub and sothat your containers can resolve internet domain names.
Save and close the file.
Restart the Docker daemon.
Verify that Docker can resolve external IP addresses by trying to pull animage:
If necessary, verify that Docker containers can resolve an internal hostnameby pinging it.
Disable dnsmasq
Ubuntu
If you prefer not to change the Docker daemon’s configuration to use a specificIP address, follow these instructions to disable dnsmasq in NetworkManager.
Edit the
/etc/NetworkManager/NetworkManager.conffile.Comment out the
dns=dnsmasqline by adding a#character to the beginningof the line.Save and close the file.
Restart both NetworkManager and Docker. As an alternative, you can rebootyour system.
RHEL, CentOS, or Fedora
To disable dnsmasq on RHEL, CentOS, or Fedora:
Disable the
dnsmasqservice:Configure the DNS servers manually using theRed Hat documentation.
Allow access to the remote API through a firewall
If you run a firewall on the same host as you run Docker and you want to accessthe Docker Remote API from another host and remote access is enabled, you needto configure your firewall to allow incoming connections on the Docker port,which defaults to 2376 if TLS encrypted transport is enabled or 2375otherwise.
Two common firewall daemons areUFW (Uncomplicated Firewall) (oftenused for Ubuntu systems) and firewalld (often usedfor RPM-based systems). Consult the documentation for your OS and firewall, butthe following information might help you get started. These options are fairlypermissive and you may want to use a different configuration that locks yoursystem down more.
UFW: Set
DEFAULT_FORWARD_POLICY='ACCEPT'in your configuration.firewalld: Add rules similar to the following to your policy (one forincoming requests and one for outgoing requests). Be sure the interface namesand chain names are correct.
Your kernel does not support cgroup swap limit capabilities
On Ubuntu or Debian hosts, You may see messages similar to the following whenworking with an image.
This warning does not occur on RPM-based systems, which enable thesecapabilities by default.
If you don’t need these capabilities, you can ignore the warning. You can enablethese capabilities on Ubuntu or Debian by following these instructions. Memoryand swap accounting incur an overhead of about 1% of the total available memoryand a 10% overall performance degradation, even if Docker is not running.
Install Docker On Redhat 5
Log into the Ubuntu or Debian host as a user with
sudoprivileges.Edit the
/etc/default/grubfile. Add or edit theGRUB_CMDLINE_LINUXlineto add the following two key-value pairs:Save and close the file.
Update GRUB.
If your GRUB configuration file has incorrect syntax, an error occurs.In this case, repeat steps 2 and 3.
The changes take effect when the system is rebooted.
Next steps
Install Docker On Redhat 7.9
- Take a look at the Get started training modules to learn how to build an image and run it as a containerized application.
- Review the topics in Develop with Docker to learn how to build new applications using Docker.
